LASER COMPONENTS News Center
+ News. There is always something new to report at LASER COMPONENTS. In our news area we keep everyone posted who is interested in our company and its services, or products. For each release you will also find the corresponding pictures in printable resolution.
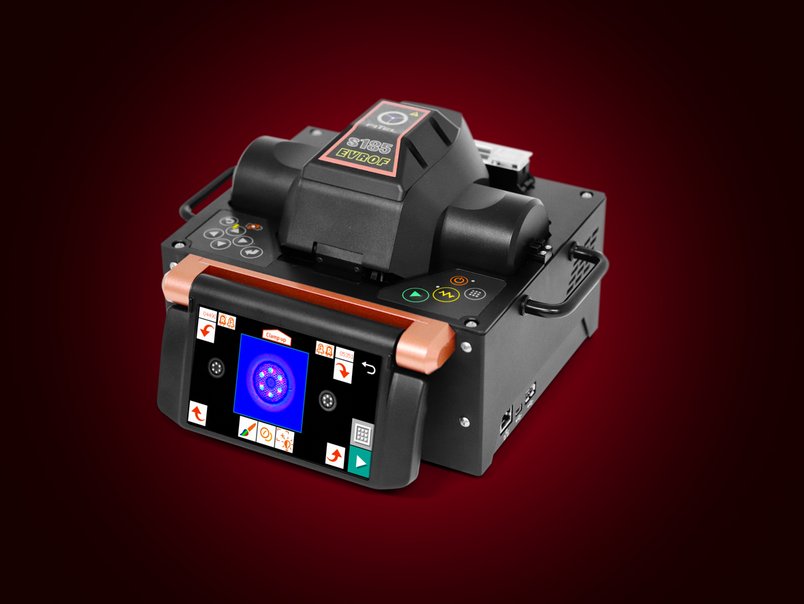
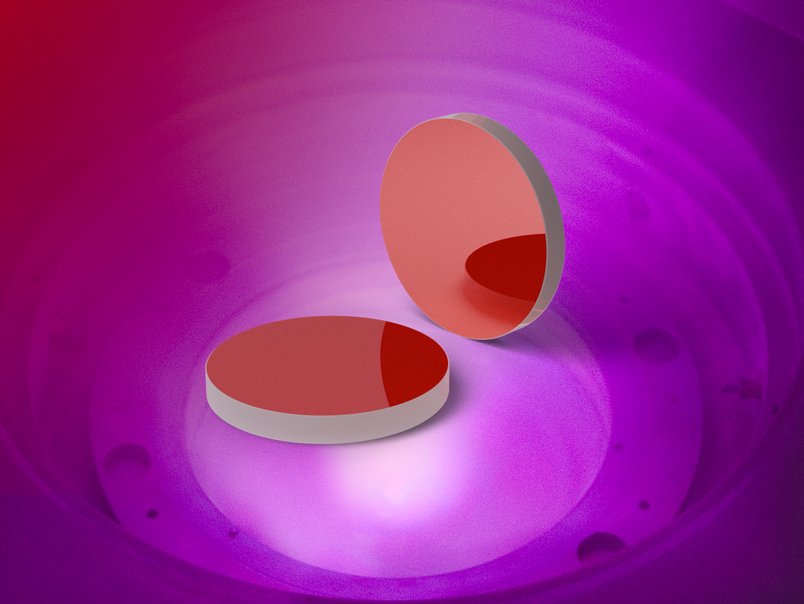
Company News Detectors Emitters Optics Fiber Optics Laser Accessories Measurement Devices


























LASER COMPONENTS Germany - Your competent partner for optical and optoelectronic components in Germany.
Welcome to LASER COMPONENTS Germany GmbH, your expert for photonics components. Each product in our wide range of detectors, laser diodes, laser modules, optics, fiber optics, and more is worth every Euro (€/EUR). Our customized solutions cover all conceivable areas of application: from sensor technology to medical technology. You can reach us here:
Werner-von-Siemens-Str. 15
82140 Olching
Deutschland
Phone: +49 8142 2864-0
Email: info(at)


